You are likely looking at outsourcing because the pressure has stacked up from three directions at once. Labor is expensive. Coverage expectations don’t stop at business hours. And the internal team you trust is already carrying more operational complexity than the org admits.
That’s when call center outsourcing services start to look less like a procurement category and more like a capacity decision. In some cases, they are the right move. In others, they create a second operation you now have to manage, govern, and defend.
The market size tells you this isn’t a niche tactic anymore. The global call and contact center outsourcing market reached USD 102.59 billion in 2024 and is projected to reach USD 242.80 billion by 2034, reflecting a broader shift toward specialized providers for cost control, scalability, and access to expertise, according to Precedence Research’s call and contact center outsourcing market analysis. The growth makes sense. Most leadership teams aren’t asking whether external support is acceptable. They’re asking where it fits without creating customer, compliance, or brand risk.
If you need a broad market-level primer before you narrow your model, this detailed guide to call center outsourcing services is a useful companion resource.
Introduction Outsourcing as a Strategic Imperative
Experienced operators often make a mistake when they first revisit outsourcing. They frame it as a staffing decision.
It isn’t. It’s an operating model decision.
Once an external partner touches your customers, systems, scripts, QA process, and escalation paths, you’ve changed how service gets delivered. You’ve also changed where accountability sits when things go wrong. If the outsourced team mishandles authentication, misses a regulated disclosure, or escalates too slowly during a service event, your customer won’t separate your brand from the vendor’s execution.
Why the old cost narrative is too narrow
The simple pitch is familiar. Lower labor rates. Faster access to coverage. Less infrastructure to manage.
Those can all be true. They’re also incomplete.
A strong outsourcing program gives you:
Elastic capacity when demand moves faster than internal hiring can keep up
Specialized operational support for after-hours, overflow, multilingual, or transaction-heavy queues
Technology advantage when the provider brings mature routing, WFM, QA, and reporting capabilities
Managerial focus by offloading activities that don’t need to stay in-house
A weak outsourcing program gives you the opposite:
Fragmented accountability
Inconsistent customer experience
Compliance exposure
A hidden layer of vendor management work your internal team didn’t budget for
Outsourcing works when leaders treat the vendor like an extension of operations, not a relief valve for headcount pressure.
What experienced leaders need to decide
The key question isn’t “Should we outsource?” It’s “Which work should move, under what controls, and with what governance?”
That means you need clarity on four points before you sign anything:
What customer interactions are safe to externalize
What knowledge and judgment still need internal ownership
What compliance controls must follow the work
What performance evidence you’ll require before expanding scope
Most failed outsourcing decisions aren’t caused by bad intent. They come from vague scope, poor risk segmentation, and contracts that lock in a delivery model before the operating model is fully defined.
Decoding Call Center Outsourcing Models
Not all call center outsourcing services solve the same problem. Some reduce labor cost. Some improve coverage. Some help you launch faster in a new queue or geography. Some move pain from one team to another.
The useful way to evaluate models is to separate delivery geography from operating structure.

Geographic delivery choices
The first layer is where the work gets done.
| Model | Where it fits | Main advantage | Main trade-off |
|---|---|---|---|
| Onshore | Regulated, high-empathy, brand-sensitive work | Better alignment on language, culture, and oversight | Higher cost |
| Nearshore | Coverage expansion with closer time-zone alignment | Easier collaboration and operational coordination | Quality varies by market and vendor maturity |
| Offshore | High-volume transactional work and scale-heavy environments | Lowest labor-cost profile in many cases | Greater governance burden and longer operational distance |
Onshore tends to work best when your legal, compliance, or brand teams need tighter control. It’s also easier when the operation depends on nuanced language, complex account handling, or close coordination with internal departments.
Nearshore sits in the middle. For many teams, it’s the most practical compromise because leaders can preserve some cost advantage without creating the full distance of an offshore model.
Offshore can still be a strong fit, but only when the work is designed for it. Standardized workflows, clear scripts, stable policy logic, and strong QA discipline matter more there than in any slide deck a vendor will show you.
Operating structure choices
The second layer is how much responsibility you hand over.
Full BPO
This is the broadest transfer. The partner handles staffing, management, and day-to-day execution for a defined scope.
It works when the process is stable and leadership is comfortable managing outcomes instead of activities. It fails when the client still wants to direct the floor hour by hour but hasn’t retained the people to do that work.
Selective outsourcing
This model keeps core functions in-house and externalizes specific workloads. Common examples include overflow, after-hours support, Tier 1 contacts, seasonal spikes, or outbound programs.
For most organizations, this is the safest way to start. It gives the internal team comparison data and protects the highest-risk interactions from moving too early.
Blended operations
This is the most operationally demanding model and frequently the most effective. Internal and outsourced agents work against the same service goals, often inside the same platform environment.
It requires stronger workforce planning, common QA standards, consistent knowledge management, and very clear escalation rules. When those pieces are in place, blended models let leaders keep strategic control while expanding capacity.
Practical rule: Don’t choose a geography first. Choose the work profile first, then find the geography and staffing structure that can support it.
What operators often overlook
A lot of teams compare models only by labor cost. That misses important variables:
Workflow complexity
Tolerance for policy errors
Need for supervisor intervention
Brand sensitivity of each interaction type
System access requirements
How often scripts and procedures change
If your process changes every week, offshore won’t save you if retraining never catches up. If your work is highly repetitive and tightly controlled, a selective offshore or nearshore model may perform well. If your customers are calling about money, health, claims, fraud, or retention, the location debate matters less than the maturity of the controls.
The Business Case Benefits Versus Hidden Risks
The upside of outsourcing is real. So are the liabilities.
Leaders often hear the upside first, and it’s not wrong. Companies using outsourcing often achieve 40 to 60 percent reductions in operational expenses, and adoption is especially high in telecom at 78 percent and financial services at 72 percent. Those sectors are useful examples because they don’t outsource casually. They do it while carrying service expectations and regulatory pressure.

Where outsourcing creates real value
The strongest business case often comes from one of four conditions.
Capacity volatility
If volume moves sharply by season, promotion, outage, or claims event, internal hiring often lags behind demand. A provider with established recruiting and management infrastructure can absorb that variability better than an internal team starting from zero.
Coverage gaps
Many organizations don’t need a full external operation. They need nights, weekends, overflow, or multilingual support without rebuilding their entire workforce model.
Specialized management muscle
Some providers bring mature operational disciplines that internal teams lack time to build. Better queue management, stronger QA rigor, established training teams, and more disciplined scheduling can matter as much as labor cost.
Technology and operational overhead
When a partner already has routing, WFM, reporting, QA, and supervisor tooling in place, your organization may avoid standing up a parallel stack just to support one line of business or region.
Where the business case breaks down
The hidden risk is simple. Leaders assume service work is transferable when the primary constraint is judgment, not volume.
The common failure points look like this:
Data governance weakness in shared or multi-tenant environments
Brand drift when agents use the script but miss the tone
Slow escalations because the vendor’s process and your internal response model don’t match
Training decay when products, policies, or offers change faster than the partner can absorb
Reporting noise that measures activity but not customer or compliance outcomes
A vendor can hit service level and still create rework, complaints, or audit exposure. That’s why the low bid is often the expensive option.
Regulated industries carry a different risk profile
Healthcare, financial services, insurance, and similar environments need a different lens. In those settings, the question isn’t whether the partner can answer contacts. It’s whether the partner can answer them under the same control structure your internal operation would be expected to maintain.
A useful reality check is to hear operators discuss where outsourcing intersects with modern CX and technology decisions. This CTG video is worth a look:
A vendor relationship becomes risky when the client outsources execution but keeps assumptions instead of controls.
What works versus what doesn’t
What works:
Well-scoped programs
Limited initial use cases
Shared QA standards
Tight escalation ownership
Operational reviews tied to business outcomes
What doesn’t:
Lifting and shifting complex queues too early
Using one vendor for every function because procurement wants simplicity
Assuming scripts solve judgment problems
Treating outsourcing like a one-time transition instead of an operating discipline
The best outsourcing decisions improve resilience. The worst ones create a cheaper front line and a more expensive cleanup effort behind it.
A Framework for Choosing the Right Model
You need a selection method that reflects risk, not just budget. Most internal debates on call center outsourcing services stall because leaders compare vendor models before they’ve agreed on decision criteria.
The cleaner approach is to score each candidate model against three business drivers.
Regulatory and compliance posture
This category should often go first. If your environment includes sensitive health, payment, claims, lending, fraud, or identity data, the outsourcing decision starts with governance.
Content in the market often skips this point, but mismanaged compliance in healthcare or finance can create remediation costs 30 to 50 percent higher than the initial savings, which is why a risk-based selection framework matters, as noted in Vonage’s discussion of outsourcing and compliance pitfalls.
Ask questions like:
Which interactions require controlled disclosures, verification, or payment handling
Which roles need direct access to regulated systems
Can the vendor support client-specific data isolation
How will QA detect policy drift before it becomes an audit issue
Who owns breach response, customer notification, and evidence retention
If the answers are weak, stop there. Cost won’t rescue a model that creates audit risk.
Brand and customer experience sensitivity
Not every queue carries the same customer consequence.
Billing disputes, complaints, cancellations, care navigation, fraud, and vulnerable-customer contacts all require more than procedural accuracy. They need judgment, listening discipline, and a clear grasp of what your brand sounds like under stress.
A simple way to sort work is to divide it into three bands:
| Interaction type | Good outsourcing candidate | Better kept in-house |
|---|---|---|
| Routine transactional | Password resets, order status, basic account questions | Rarely necessary to keep internal |
| Guided service | Tier 1 support, appointment handling, scripted service recovery | Depends on training and QA maturity |
| High-consequence interactions | Limited use unless tightly governed | Retention, regulated disputes, complex escalations |
Many leaders overestimate script quality. A script can standardize language. It can’t replace judgment in moments where customers are confused, upset, or at risk of churn.
Keep the interactions that define trust closer to the business, at least until the partner proves they can carry them.
Financial and operational agility
This last category is where model choice becomes practical.
You’re evaluating not just the unit economics but also the effort needed to launch, manage, and adapt the operation.
Use these tests:
How fast do you need capacity? If demand is immediate, a model that needs long setup and training cycles may solve the problem too late.
How often does the process change? The more often products, policies, or promotions change, the more you need a partner who can absorb updates without service degradation.
How much management bandwidth do you have? A blended model can be strong, but only if someone internally owns calibration, reporting, and issue resolution.
What happens during failure? Every model looks good in steady state. Test it against outage periods, recall events, billing errors, and backlog conditions.
A defensible decision frequently emerges from this pattern:
Onshore or tightly governed blended models for regulated or brand-sensitive work
Nearshore selective outsourcing for coverage gaps and flexible expansion
Offshore models for standardized, lower-risk processes with disciplined controls
The point isn’t to find one universal answer. It’s to match the work to the right risk profile.
The Vendor Evaluation Checklist for Leaders
Vendor selection is where good strategy often gets diluted by demos, pricing sheets, and polished service narratives. Operators need a different filter. You’re not buying promises. You’re evaluating whether the partner can run your work under pressure.
Cloud Tech Gurus has logged extensive hours of vendor evaluation across numerous vendors and solution categories, which is enough to see a consistent pattern. Vendors rarely fail in the PowerPoint. They fail in controls, operational discipline, and the details of day-two execution.
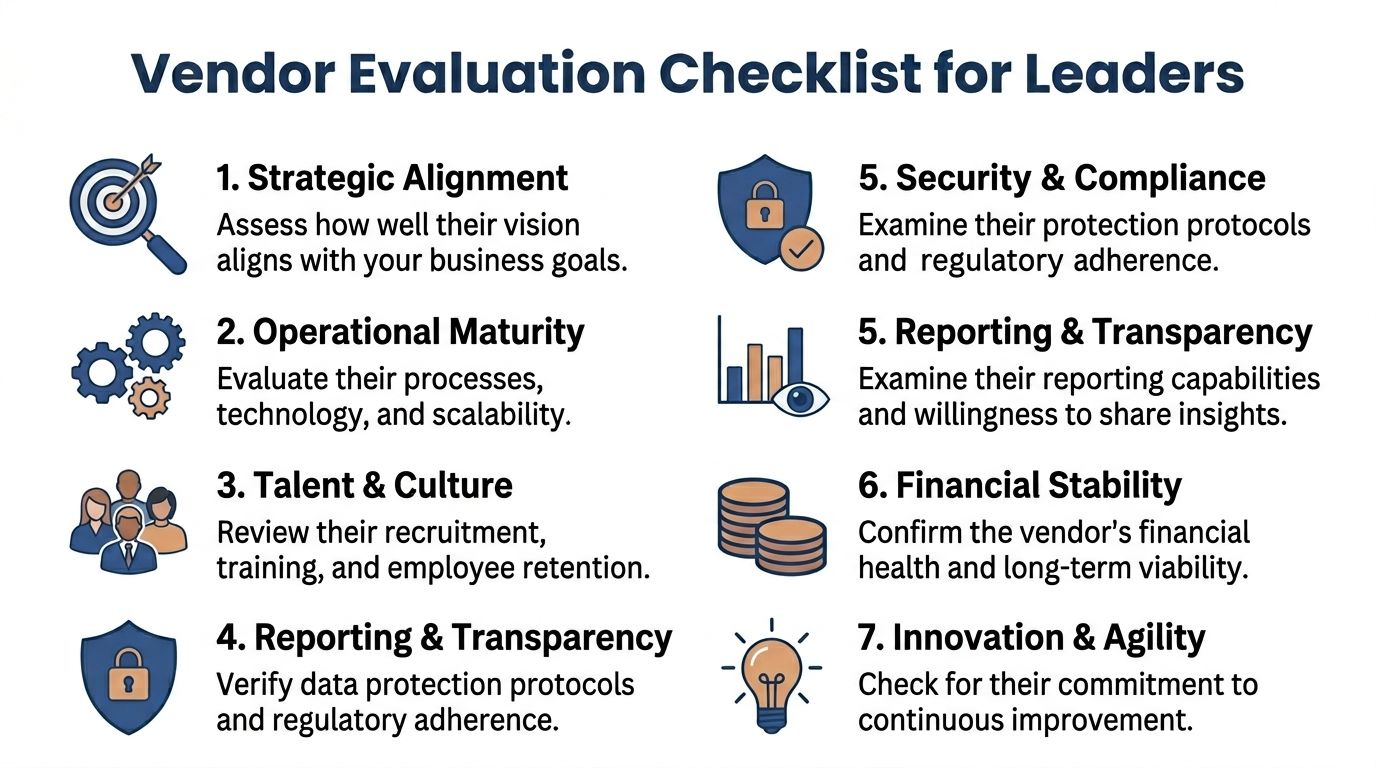
What to inspect beyond price
Use this checklist in diligence sessions, not just in the RFP.
Strategic fit
Start with scope alignment.
Can the vendor clearly state which work they should handle, which work they shouldn’t, and where the client must retain ownership? If they say yes to everything, that’s usually a warning sign.
Recruiting and training discipline
You need to know how they hire for your work, not how they hire in general.
Look for:
Role-specific recruiting logic tied to your contact types
Structured nesting and ramp plans
Calibration methods between vendor QA and your internal QA
Proof that training updates reach production quickly
If the vendor can’t explain how they keep content current, your customer will discover the gap before your scorecard does.
Security and compliance controls
For regulated environments, broad statements about security aren’t enough.
Ask to see how they manage:
Access control by client and by role
Audit logging and evidence retention
Data segregation in multi-tenant environments
Policy change management
Supervisor intervention for sensitive interactions
Leaders also need to examine AI claims carefully. Many tools sound mature in demos but aren’t built for regulated, multi-tenant environments. In healthcare, for example, AI-assisted nurse triage can reduce ER visits by 25 percent, but that result depends on specific compliance controls that generic AI tools don’t provide, as discussed by Conduit Health Partners in its nurse triage overview.
Technology reality check
A vendor’s stack matters because it shapes reporting, integration effort, agent speed, and your ability to govern performance.
Probe for specifics:
Which CCaaS, CRM, WFM, QA, and analytics tools are live today
How they integrate with your systems
Whether your team can access raw data or only curated dashboards
How quickly routing, IVR, or scripting changes can be deployed
What AI functions are in production versus planned
If you want a structured approach to this diligence, CTG’s vendor selection process is designed around operational fit, governance, and implementation realities, not just feature comparison.
Don’t ask vendors whether they support compliance. Ask them to show how they maintain it during exceptions, escalations, and rapid change.
Business continuity and transparency
This part gets less attention than it should.
You need clear answers on:
Disaster recovery
Leadership coverage
Attrition response
Back-up sites or remote continuity options
Escalation ownership during service events
Then test reporting quality. The right vendor doesn’t just send monthly scorecards. They can explain what changed, why it changed, and what action they recommend next.
The best partner behaves like an operator. The weaker one behaves like a staffing layer with a dashboard.
Your Implementation and Migration Roadmap
Signing the contract is the start of the risk, not the end of it. The migration phase is where leaders find out whether the chosen call center outsourcing services model was designed for real operations or just approved in principle.
The main mistake is compressing transition work into a training schedule. A proper launch needs process design, governance, system readiness, and controlled exposure.
Phase one gets the work ready
Before a single agent takes a live contact, the client and partner need a common operating baseline. This includes:
Process maps that reflect the actual workflow, not the ideal one
Knowledge documentation with current policy, exception handling, and escalation logic
Call types segmented by complexity and risk
Definition of what the vendor can decide versus what must come back to the client
The weakest transitions rely on tribal knowledge. If your internal supervisors carry the operation in their heads, the outsourced team will inherit only fragments.
Phase two connects systems and controls
Technology integration is rarely the hardest technical task, but it’s often the hardest operational one. Access rules, disposition structure, call recording, QA workflows, and reporting definitions all have to match how the business will govern the work.
This is also where timeline realism matters. Full offshore operational setup can take up to 7 months, while nearshore partners may ramp in 2 to 3 months, and hybrid models can use AI virtual agents for immediate Tier 1 support to cover gaps during transition, according to Flairstech’s discussion of AI-enabled technical support outsourcing.
If you need help coordinating that transition, CTG’s implementation support is one option for aligning requirements, vendor workstreams, and operational readiness.
Phase three pilots before scale
Don’t go live with the full volume if you can avoid it.
Use a pilot to test:
Training absorption
Escalation speed
Knowledge accuracy
QA calibration
Reporting integrity
Customer response to the new team
The pilot should include edge cases, not just easy contacts. If the team performs only on straightforward transactions, you still don’t know whether the model is ready.
Launch small enough to learn, but broad enough to expose operational weakness.
Phase four manages internal change
Outsourcing changes internal roles. Supervisors become calibrators. Analysts spend more time validating vendor reporting. Operations leaders shift from direct floor management to performance governance.
That change needs explicit ownership.
A good migration plan assigns named leaders to:
Training sign-off
Knowledge management
Escalation management
Scorecard validation
Business review cadence
What fails most often isn’t the vendor’s ability to answer contacts. It’s the client’s lack of governance after launch.
Measuring Success with the Right KPIs and SLAs
A lot of outsourced programs get measured with the wrong scorecard. They track average speed, handle time, and top-line service level, then act surprised when complaints, compliance defects, or repeat contacts rise.
Good governance starts with a balanced view of performance.

What should be on the scorecard
You need measures across four groups.
Customer outcome metrics
These tell you whether customers are getting resolution.
Include:
First contact resolution
Repeat contact rate
Escalation rate
Customer satisfaction or similar post-contact feedback
Quality and compliance metrics
These protect the business when efficiency metrics look fine but execution is drifting.
AI-powered quality assurance can review 100 percent of calls, versus 5 to 10 percent sampling by human managers, detecting compliance issues and sentiment shifts in real time and reducing escalations by 28 percent, according to TDS Global Services on AI in call centers.
That matters because outsourced operations often hide risk in the unreviewed portion of contacts. If your QA process only sees a sample, your SLA can look healthy while policy errors spread.
For teams refining supervisor oversight and live coaching, these monitor, coach, and barge features are worth understanding because they shape how quickly leaders can intervene in active interactions.
Build SLAs that define behavior, not just speed
The contract should specify more than target numbers.
It should define:
| SLA element | What to clarify |
|---|---|
| Metric definition | Exactly how each KPI is calculated |
| Data source | Which system is the system of record |
| Measurement cadence | Daily, weekly, monthly, and rolling-period views |
| Exception rules | What gets excluded and why |
| Remedies | What happens when performance misses target |
| Escalation path | Who intervenes, and how fast |
Here, many teams lose influence. If the SLA leaves room for interpretation, every miss becomes a debate instead of a corrective action.
If you’re building a stronger ongoing oversight model, CTG’s workforce and quality management perspective is relevant because outsourced accountability usually breaks where quality, forecasting, and coaching aren’t connected.
A useful SLA doesn’t just report underperformance. It makes recovery actions automatic.
What a mature review cadence looks like
Monthly business reviews aren’t enough on their own.
Strong governance typically includes:
Weekly operational reviews for service, quality, and backlog
Regular calibration sessions between internal QA and vendor QA
Change-control meetings for policy, product, or workflow updates
Quarterly strategic reviews to decide whether scope should expand, contract, or stay stable
If the partnership is working, your scorecard should tell you more than whether the vendor is busy. It should tell you whether customers are getting the right outcome at the right risk level.
Conclusion Your Next Steps in Outsourcing
Call center outsourcing services can reduce cost, expand capacity, and add operational flexibility. None of that matters if the model creates customer friction, compliance exposure, or weak accountability.
The right decision frequently comes from disciplined segmentation. Keep high-risk work close. Externalize what can be standardized and governed. Evaluate vendors on controls, operating maturity, and transparency, not just labor economics. Then manage the partnership with a scorecard that protects the business, not one that only reports speed.
This is why experienced operators treat outsourcing as a long-term operating decision. Not a sourcing event.
Cloud Tech Gurus provides vendor-neutral, practitioner-led consulting for contact center and CX leaders. Learn more at cloudtechgurus.com.